If you’re connecting several Docker containers using the standard “bridge” network, you might hit a common limitation: Docker’s default bridge network doesn’t provide name resolution (DNS), nor does it allow you to assign fixed IP addresses to containers in the virtual network. These limitations are outlined in the Docker documentation. Fortunately, there’s an easy fix! You can create your own custom bridge network to bypass these issues.
Quick Guide: Creating Your Own Bridge Network
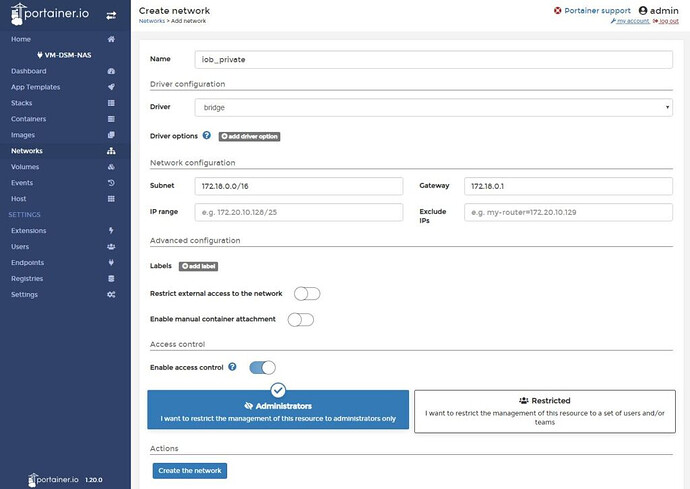
- Open the Portainer web interface and navigate to the “Networks” section.
- Click on “Add network” to open a form.
- Assign a meaningful name to the network. In this example, we’ll call it “iob_private” (to complement the “iob_public” MACVLAN from another tutorial). This network will be used for internal Docker communication.
- For the “Driver,” select “bridge” since this is the network type we’re creating.
- Under “Network configuration,” set the “Subnet” and “Gateway.” In this case, we’ll use
172.18.0.0/16as the subnet and172.18.0.1as the gateway to mirror the default bridge network. - Leave the “Advanced configuration” settings off. This section allows you to limit the network to internal traffic only, but since we might want to expose certain ports (e.g., from a database container), we’ll leave it as is.
- Skip the “Enable manual container attachment” option as it’s unnecessary.
- The “Access Control” settings are optional and only impact permissions within Portainer, so configure this based on your preferences.
- Finally, click “Create the network” to complete the setup. Your custom bridge network is now ready to use!
Using Docker-Compose (aka “Portainer Stacks”)…
You can also define a custom bridge network in your docker compose file, which is called a “Stack” in Portainer. If you’re unfamiliar with Stacks, you can [learn more here]. For those familiar with Docker Compose, here’s an example based on the steps above. The network name in this example is “internal”:
networks:
internal:
driver: bridge
ipam:
config:
- subnet: 172.18.0.0/16
gateway: 172.18.0.1
ip_range: 172.18.0.1/24
This configuration will create a custom network for your containers with fixed IP ranges and routing, making it easier to manage internal communication between your containers while maintaining flexibility for external access when needed.