The discussion surrounding Cross-Origin Resource Sharing (CORS) often leads to misconceptions regarding the origin of the headers involved. This confusion can be alleviated by understanding the underlying principles of the Same Origin Policy (SOP) and the role of CORS in web security.
Understanding the Same Origin Policy
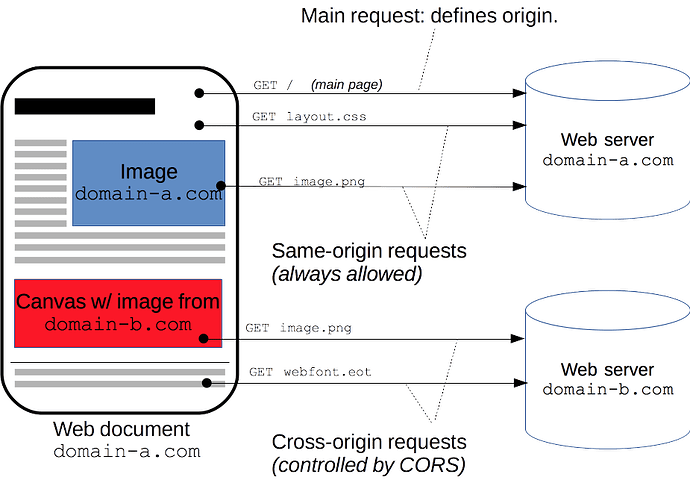
The Same Origin Policy is a critical security measure implemented in web browsers that restricts how documents or scripts from one origin can interact with resources from another origin. An origin is defined as a combination of the scheme (protocol), host (domain), and port. For instance, https://example.com:443 is a distinct origin from http://example.com:80.
Purpose of the Same Origin Policy
The primary purpose of the SOP is to prevent malicious scripts on one website (e.g., siteA.com) from accessing sensitive information on another site (e.g., siteB.com). Without this policy, a script from siteA.com could potentially send requests to siteB.com using the user’s authentication credentials, thereby compromising user data.
The Role of CORS
In scenarios where cross-domain interactions are necessary, CORS serves as a mechanism to relax the restrictions imposed by SOP. CORS allows servers to specify who can access their resources through the use of specific HTTP headers, most notably the Access-Control-Allow-Origin header.
How CORS Works
When a web application hosted on one domain (e.g., domainA.com) attempts to request resources from another domain (e.g., domainB.com), the browser sends an HTTP request that includes an Origin header indicating the source of the request. The server at domainB.com then responds with an appropriate Access-Control-Allow-Origin header, which specifies whether or not the requesting domain is permitted to access its resources.
For example:
Access-Control-Allow-Origin: https://domainA.com
This header explicitly allows requests from domainA.com. Alternatively, using:
Access-Control-Allow-Origin: *
indicates that any domain can access the resource, which is commonly used for public APIs.
Determining Header Ownership
A common source of confusion arises when considering which domain should serve CORS headers. To illustrate this, consider a scenario where a user visits a potentially harmful site (malicious.com) that attempts to make cross-origin requests to a secure site (mybank.com). It is imperative that mybank.com controls its own CORS policy and decides whether to allow requests from malicious.com. If malicious.com were allowed to dictate its own CORS headers, it could effectively bypass SOP protections, leading to significant security vulnerabilities.
Developer Perspective
Developers often mistakenly approach CORS from their own site’s perspective, believing they should dictate which external sites can interact with their resources. However, it is crucial to shift this mindset and consider which external scripts may attempt to access your site’s resources. This perspective ensures that security measures are appropriately applied and that only trusted origins are granted access.
In summary, understanding CORS and its relationship with SOP requires recognizing that while developers may control their own domains’ responses, it is ultimately up to each resource-hosting domain to set its own CORS policies in order to maintain security and integrity across web applications.